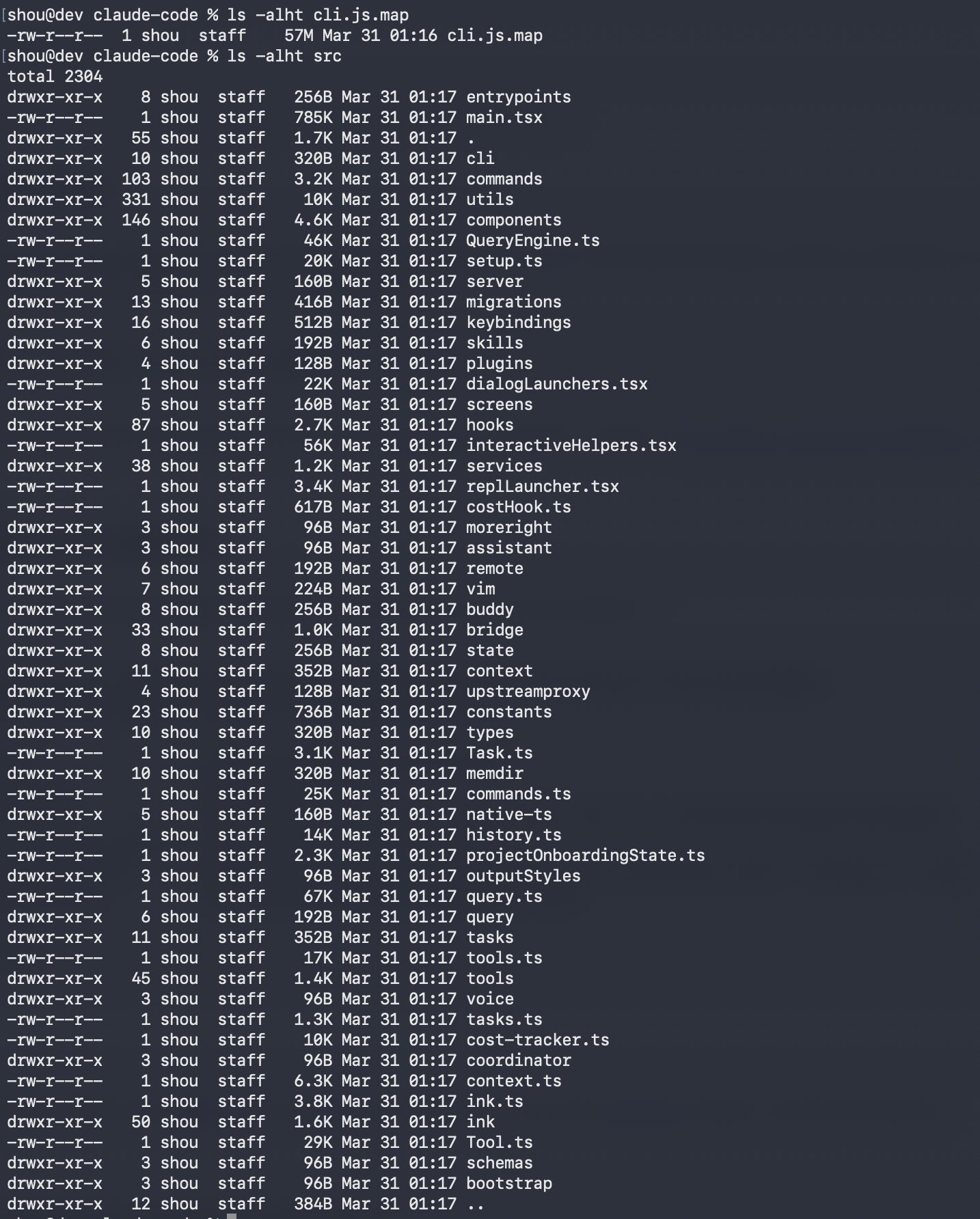
Claude Code's source code has been leaked via a map file in their NPM registry
The article details a security incident where the source code for Claude Code, likely an AI coding tool from Anthropic, was accidentally exposed via a source map file in its NPM package. This suggests a misconfiguration in the package registry, leading to the leak of proprietary code.
For a senior engineer focused on AI/ML tooling and cloud infrastructure, this underscores critical vulnerabilities in software supply chains and the importance of securing package deployments in environments like NPM and PaaS.