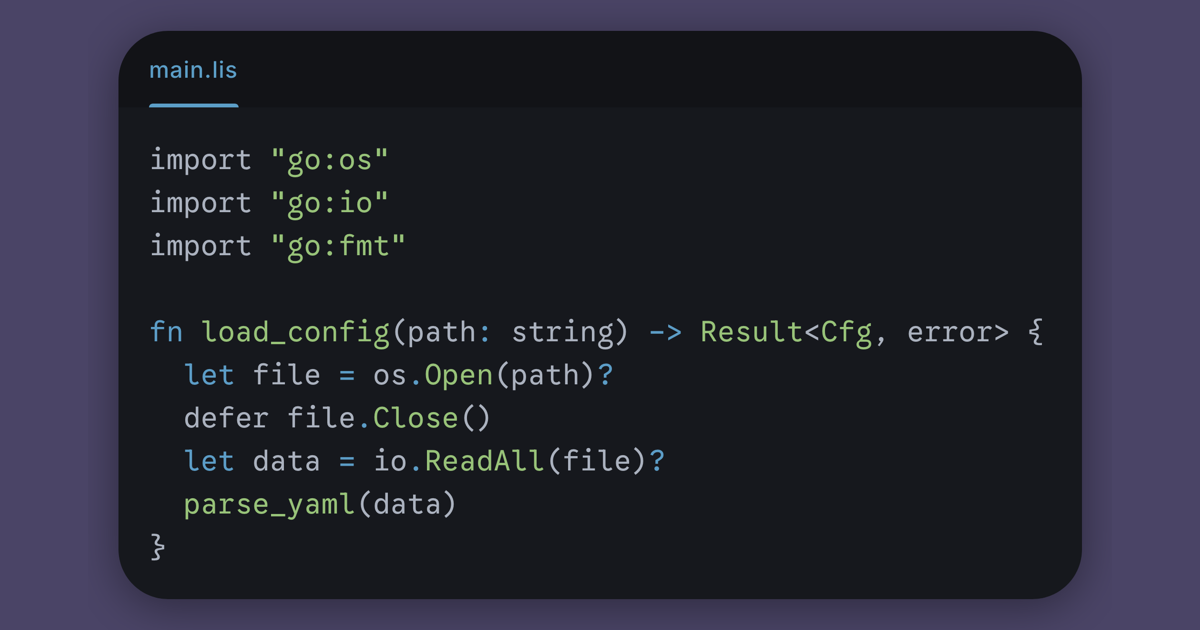
Lisette a little language inspired by Rust that compiles to Go
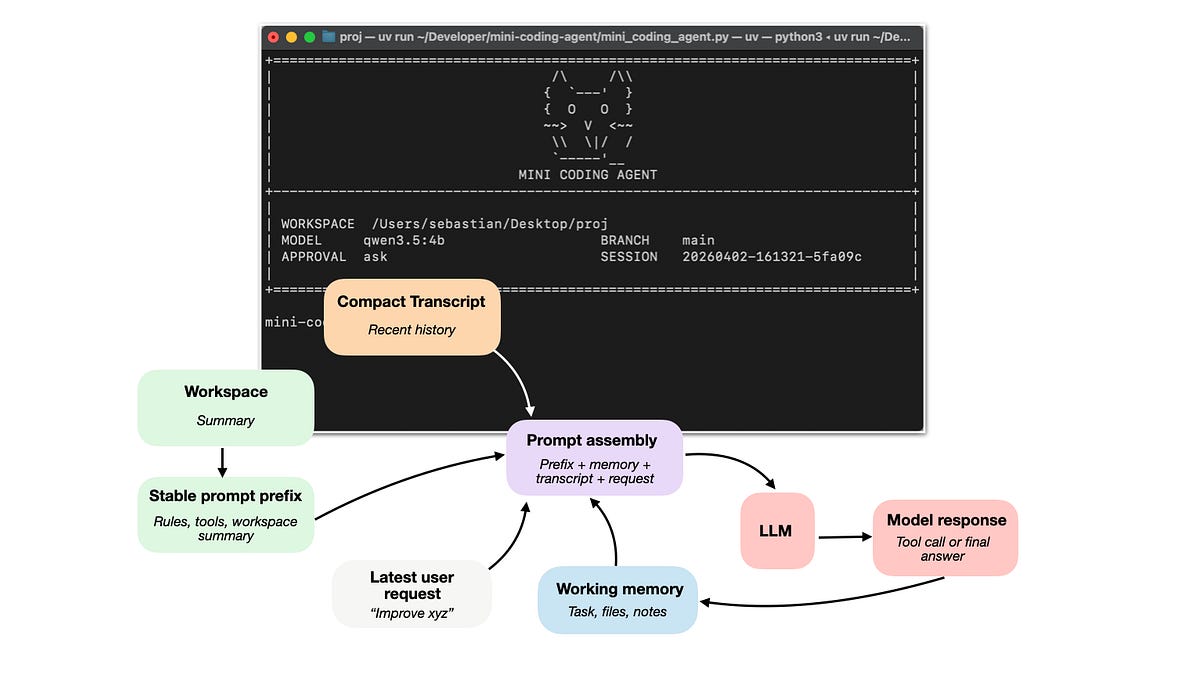
Lisette is a Rust-inspired language compiling to Go, featuring algebraic data types, pattern matching, and a Hindley-Milner type system with immutability by default and no nil pointers. It catches Go runtime issues at compile time while maintaining full interoperability with Go's ecosystem. As a senior engineer working with cloud infrastructure and developer tooling, Lisette's compile-time safety enhancements could reduce critical runtime errors in Go-based microservices or AI agent orchestration systems. Evaluate Lisette for Go projects to eliminate nil-related bugs and leverage stronger type guarantees without sacrificing ecosystem compatibility.