Why coding agents will break your CI/CD pipeline (and how to fix it)
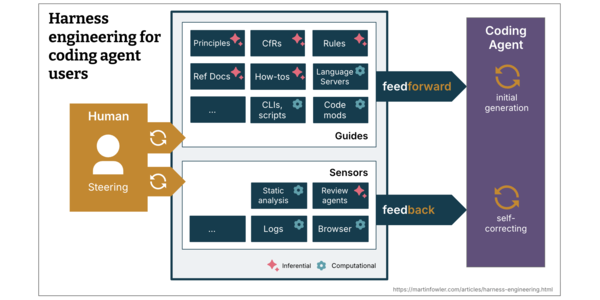
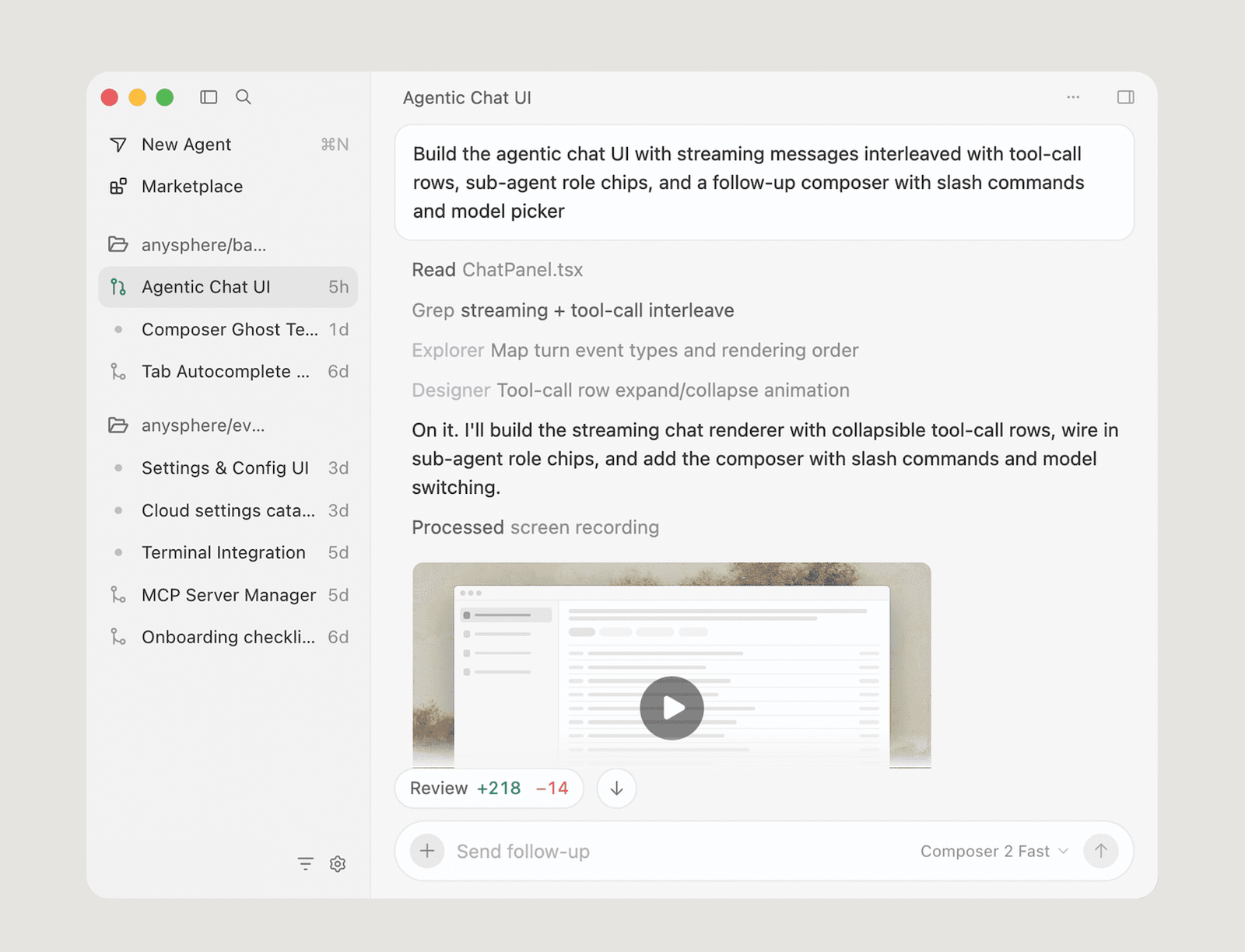
Autonomous AI agents generating 10x more code overwhelm CI/CD by shifting the bottleneck to validation; shared staging environments fail under asynchronous parallel commits, causing cascading microservice outages. Teams must implement isolated, production-like validation environments per agent to prevent deploy gaps and post-merge failures. This directly impacts your focus on AI/ML agent orchestration and cloud-native architectures, as validation bottlenecks will determine whether increased code velocity translates to safe, scalable deployment. Replace shared staging with ephemeral, agent-isolated validation environments to prevent cascading failures in microservices.